# Rick Roll
tag: easy SRPG
I hope you know your crypto basics.
flag format: pearl{string with "_"}
## Solve
Text base ciper need text base solution. I head on to
[dcode](https://www.dcode.fr/vigenere-cipher) to get "PEARLCTF" key for the
first phase
```txt
Never Gonna Give You Up
We're no strangers to love
You know the rules and so do I
A full commitment's what I'm thinking of You wouldn't get this from any other
guy I just wanna tell you how I'm
feeling Gotta make you understand
Never gonna give you up Never gonna let you down
Never gonna run around and desert you Never gonna make you cry
Never gonna say goodbye
Never gonna tell a lie and hurt you We've known each other for so long
Your heart's been aching but you're too shy to say it Inside we both know
what's been going on
evqx ebzyvbt vg qvtsvqhzg gb ibqrffgnbq
We know the game and we're gonna play it And if you ask me how I'm feeling
Don't tell me you're too blind to see Never gonna give you up
Never gonna let you down
Never gonna run around and desert you Never gonna make you cry
Never gonna say goodbye
Never gonna tell a lie and hurt you Never gonna give you up
Never gonna let you down
Never gonna run around and desert you Never gonna make you cry
Never gonna say goodbye
Never gonna tell a lie and hurt you Never gonna give, never gonna give (Give
you up)
(Ooh) Never gonna give, never gonna give (Give you up)
```
These parts not seem right, so phase 2 it is
```txt
evqx ebzyvbt vg qvtsvqhzg gb ibqrffgnbq
```
I have no ideal what this could be, but after some trier and error, `n` and
`o` as key can get me parse like this
```txt
rick rolling is ...
```
So my assumtion is that we need to make a key base on those character. I quite
give up in this step and just asumming the flag is a make sense words by
merging decrypted character with key = `n` and key = `o` and replacing the
space with `_` (Which later being told that it is ROT13.5)
\- msg : `evqx ebzyvbt vg qvtsvqhzg gb ibqrffgnbq`
\- flag: `rick_rolling_is_difficult_to_understand`
\- key : `nnonnnonnonnonnonnononnnoonnonnnon`
That right, and i also add `pearlctf{}` while hoping it the right answer,
can't really make sense the key by any mean
Original writeup (https://github.com/nghiango1/pearlctf-
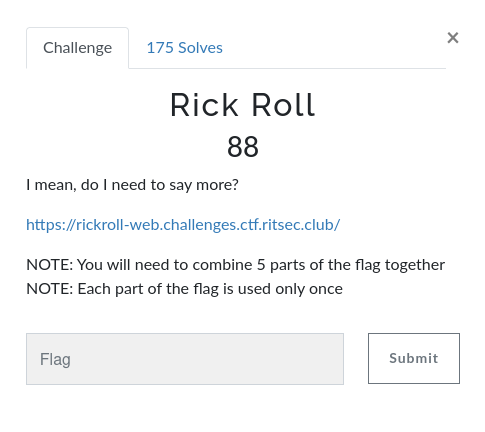
writeup/edit/main/crypto/Rick%20Roll).# Rick Roll
\- 53 Points / 343 Solves
## Background
I mean, do I need to say more?
[https://rickroll-web.challenges.ctf.ritsec.club/](https://rickroll-
web.challenges.ctf.ritsec.club/)
NOTE: You will need to combine 5 parts of the flag together
NOTE: Each part of the flag is used only once
## Find the flag
**Home page:**
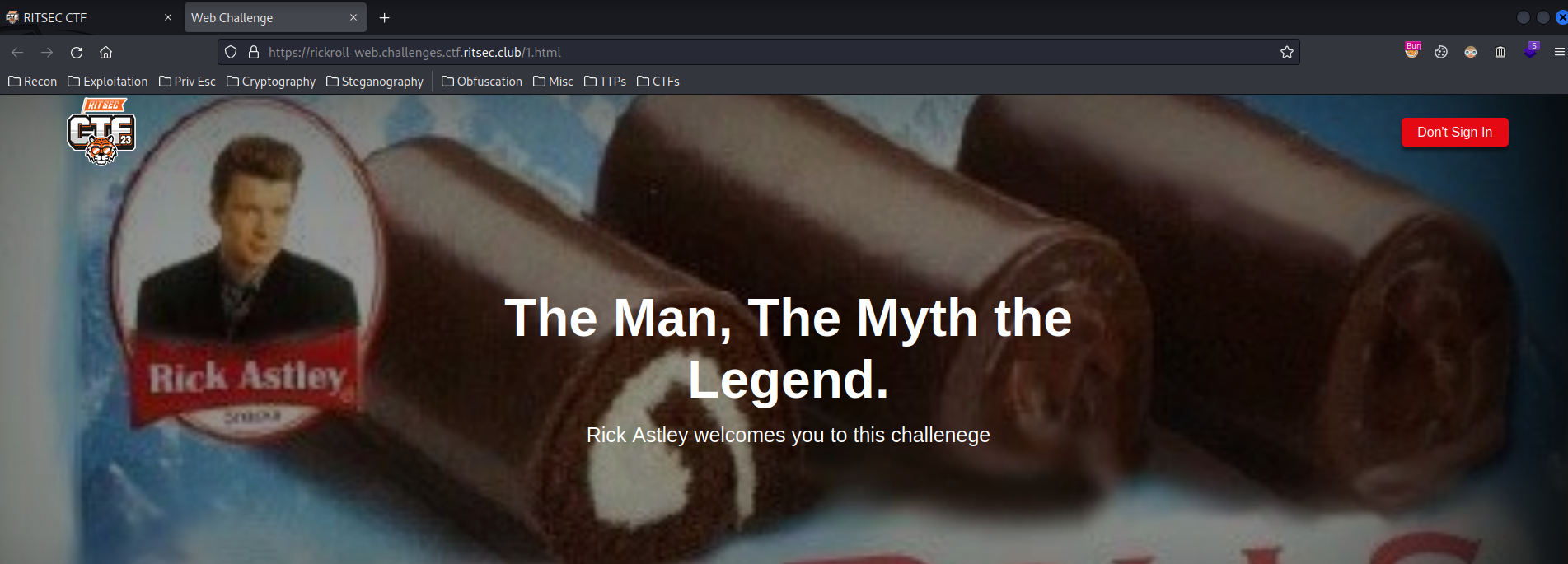
When we go to `/`, it'll redirect us to `/1.html`.
**Let's view the source page:**
```html
[...]
[...]
Don't Sign In
[...]
```
Nice rickroll.
And we found the first part of the flag!
\- `_TuRna30unD_`
We can also see that in `/1.html` there's a CSS is loaded via ``
element: **`2.css`**
```shell
┌[siunam♥earth]-(~/ctf/RITSEC-CTF-2023)-[2023.04.01|13:53:12(HKT)]
└> curl https://rickroll-web.challenges.ctf.ritsec.club/2.css
[...]
Hey there you CTF solver, Good job on finding the actual challenge, so the
task here is to find flags to complete the first half of the chorus of this
song, and you
will find the flags around this entire web network in this
format,/*[FLAG_PIECE]*/ Heres a piece to get started /*[RS{/\/eveRG0nna_]*/
find the next four parts of the famous chorus
[...]
.input button{
[...]
background-color: [_|3tY0|_|d0vvn] var(--primary-color);
[...]
}
[...]
```
We found 2 more parts!
\- `RS{/\/eveRG0nna_`
\- `_|3tY0|_|d0vvn`
**Then, in `1.html`, we also see that there's a "Don't Sign In" link:**
**Again, view source page:**
```html
[...]
[...]
```
Found the fourth one!
\- `_D3s3RTy0u}`
**Next, we also see there's a `1.css` CSS file:**
```css
[...]
.btn{
[...]
border: /*[G1v3y0uuP]*/ none;
[...]
}
[...]
.input button{
[...]
text-align: /*[_|3tY0|_|d0vvn_]*/center;
[...]
}
```
Found the last part of the flag!
\- `G1v3y0uuP`
**Hence, the full flag will be:**
\- **Flag: `RS{/\/eveRG0nna_G1v3y0uuP_|3tY0|_|d0vvn_TuRna30unD__D3s3RTy0u}`**
## Conclusion
What we've learned:
1\. Inspecting Source Pages
Original writeup (https://siunam321.github.io/ctf/RITSEC-CTF-2023/Web/Rick-
Roll/).